EC-Council Certified Penetration Testing Professional / CPENTv2
The Certified Penetration Professional, or CPENT for short, is simply the new standard in training for future penetration testers. The Certified Penetration Professional (CPENT) course program of the Council of E-Commerce (EC-Council) imparts the necessary knowledge to attack a company network during a penetration test, exploit vulnerabilities (exploitation) and at the same time circumvent IT security countermeasures (evasion). Finally, the course shows suitable countermeasures to protect the affected system.
Anyone who has previously worked mainly in flat office communication networks (client to server) will develop their own skills far beyond these limits in the extensive network infrastructure (practice range) of the course. This includes, among other things, attacking IoT (Internet of Things) and OT (operation technology; industrial automation) systems, writing your own exploits and building your own tools (which can be used in the practical exam). The training also includes the implementation of binary exploits (pwning) and double pivoting to access hidden or isolated networks. The training is rounded off by the individualization of existing scripts and exploits in order to extract even the last secrets from the target networks.
Certification, one exam - CPENT & LPT Master
You have the opportunity to acquire two certifications with one exam. If you achieve more than 90% in the CPENT live range exam, you will not only receive the CPENT certification, but also the title of Licensed Penetration Tester (LPT) Master!
Exam options:
- Choose your challenge! Either two 12-hour exams or a single 24-hour exam!
- EC-Council specialists oversee the entire exam
- Score at least 70% and become a CPENT
- Score at least 90% and you will be awarded the highly respected LPT (Master) title.
- Module 1: Introduction to Penetration Testing and Methodologies
- Module 2: Penetration Testing Scoping and Engagement
- Module 3: Open Source Intelligence (OSINT) and Attack Surfcae Mapping
- Module 4: Social Engineering Penetration Testing
- Module 5: Web Application Penetration Testing
- Module 6: API and Java Penetration Testing
- Module 7: Perimeter Defense Evasion Techniques
- Module 8: Windows Exploitation and Privilege Escalation
- Module 9: Active Directory Penetration Testing
- Module 10: IoT Penetration Testing
- Module 11: Linus Exploitation and Privilege Escalation
- Module 12: Reverse Engineering, Fuzzing and Binary Exploitation
- Module 13: Lateral Movement and Pivoting
- Module 14: Report Writing and Post Testing Actions
Self-Study Module
- Module 1: Penetration Testing Essential Concepts
- Module 2: Mastering Metasploit Framework
- Module 3: PowerShell Scripting
- Module 4: Bash Environment and Scripting
- Module 5: Python Environment and Scripting
- Module 6: Perl Environment and Scripting
- Module 7: Ruby Environment and Scripting
- Module 8: Wireless Penetration Testing
- Module 9: OT and SCADA Penetration Testing
- Module 10: Cloud Penetration Testing
- Module 11: Database Penetration Testing
- Module 12: Mobile Device Penetration Testing
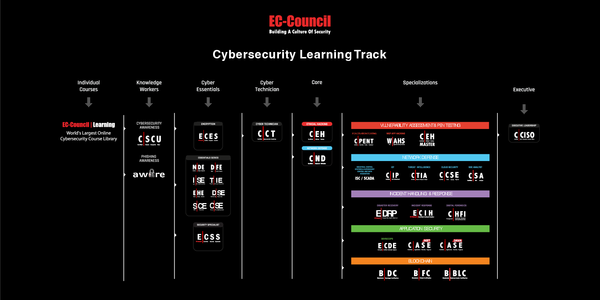
- Certified Ethical Hacker (CEH) course
- Advanced knowledge of network protocols
- Knowledge of Kali or ParrotOS and common penetration testing tools
- Knowledge of using Windows and Linux hosts
- Knowledge of Pivilege Escalation on Linux and Windows
- Knowledge of wireless penetration testing
- Knowledge of web application penetration testing
- Knowledge of English: Since the course materials and the exam are only available in English, solid written English skills are required